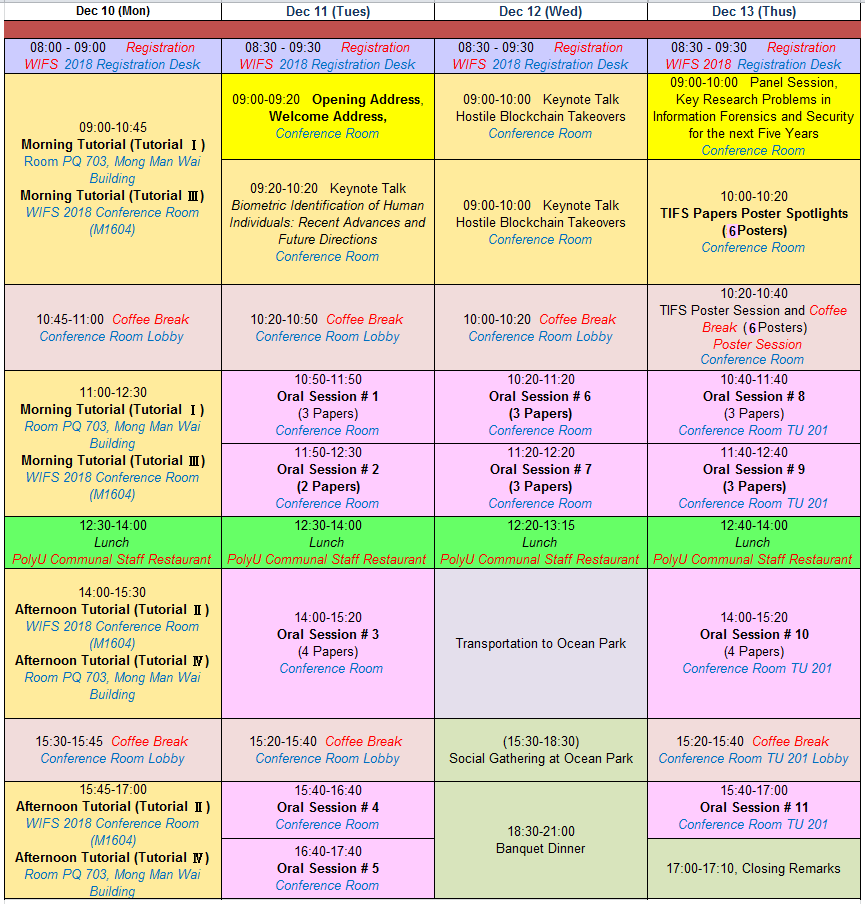
Detailed Program
Download Conference Program :
Booklet
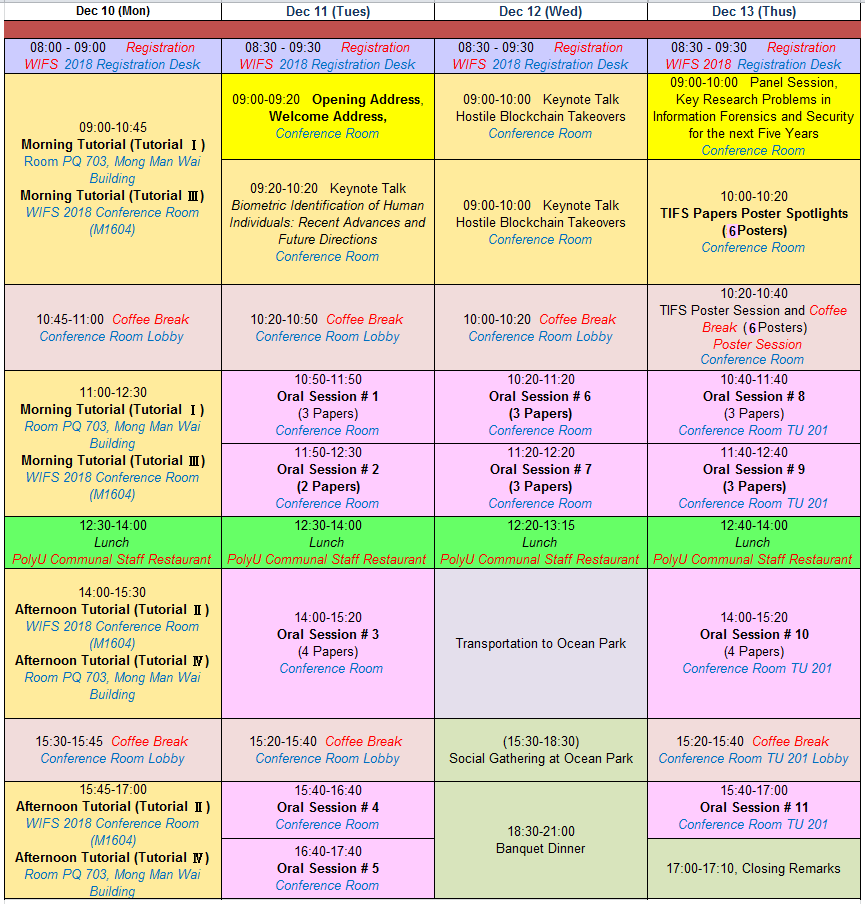
December 10, 2018
Registration (08:00 - 09:00)
Venue: Registration Desk, Reception Area (M1607, Li Ka Shing Tower)
Morning Tutorial (Tutorial I) (09:00 - 12:30)
Privacy-Aware Smart Metering
Presenters: Deniz Gunduz (Imperial College London, London, UK)
Tobias Oechtering (KTH Royal Institute of Technology, Stockholm, Sweden)
Venue: Room PQ 703, Mong Man Wai Building
Morning Tutorial (Tutorial III) (09:00 - 12:30)
Role of Adversaries in Deep Learning
Presenters: Mayank Vatsa (IIIT Delhi, India), Richa Singh (IIIT Delhi, India)
Venue: WIFS 2018 Conference Room (M1604, Li Ka Shing Tower)
Coffee break (10:45-11:00)
Venue: Reception Area (M1607, Li Ka Shing Tower)
Morning Tutorial (Tutorial I, Contd.) (11:00 - 12:30)
Privacy-Aware Smart Metering
Presenters: Deniz Gunduz (Imperial College London, London, UK)
Tobias Oechtering (KTH Royal Institute of Technology, Stockholm, Sweden)
Venue: Room PQ 703, Mong Man Wai Building
Morning Tutorial (Tutorial III, Contd.) (11:00 - 12:30)
Role of Adversaries in Deep Learning
Presenters: Mayank Vatsa (IIIT Delhi, India), Richa Singh (IIIT Delhi, India)
Venue: WIFS 2018 Conference Room (M1604, Li Ka Shing Tower)
Lunch (12:30 -14:00)
Venue: PolyU Staff Restaurant (4/F, Communal Building)
Afternoon Tutorial (Tutorial II) (14:00 - 17:00)
Privacy- Location Privacy: Threats and Opportunities
Presenters: Fernando Pérez-González (University of Vigo, Spain)
Simón Oya (University of Vigo, Spain)
Venue: WIFS 2018 Conference Room (M1604, Li Ka Shing Tower)
Afternoon Tutorial (Tutorial IV) (14:00 - 17:00)
Biometric Template Protection and Evaluation
Presenters: Marta Gomez-Barrero (Hochschule Darmstadt, Germany)
Venue: Room PQ 703, Mong Man Wai Building
Coffee break (15:30 - 15:45 )
Venue: Reception Area (M1607, Li Ka Shing Tower)
Afternoon Tutorial (Tutorial II, Contd.)(15:45 - 17:00)
Privacy- Location Privacy: Threats and Opportunities
Presenters: Fernando Pérez-González (University of Vigo, Spain), Simón Oya (University of Vigo, Spain)
Venue: WIFS 2018 Conference Room (M1604, Li Ka Shing Tower)
Afternoon Tutorial (Tutorial IV, Contd.)(15:45 - 17:00)
Biometric Template Protection and Evaluation
Presenters: Marta Gomez-Barrero (Hochschule Darmstadt, Germany)
Venue: Room PQ 703, Mong Man Wai Building
December 11, 2018
Registration (08:30 - 09:30)
Venue: Registration Desk, Reception Area (M1607)
Welcome Session (09:00-9:20)
Opening Address
Welcome Address
Venue: Conference Room
Keynote Talk (09:20 -10:20)
Keynote Speaker: Tieniu Tan (Center for Research on Intelligent Perception and Computing National Laboratory of
Pattern Recognition, Institute of Automation, Chinese Academy of Sciences (CAS), Beijing, China)
Biometric Identification of Human Individuals: Recent Advances and Future Directions
Venue: Conference Room
Coffee break (10:20 -10:50)
Venue: Conference Room Lobby
Oral Session # 1 - Audio and Video Forensics (10:50-11:50 AM)
Session Chair: Chang-Tsun Li (University of Warwick, UK)
Venue: Conference Room
In Ictu Oculi: Exposing AI Created Fake Videos by Detecting Eye Blinking(10:50-11:10 AM)
Yuezun Li (University at Albany, State University of New York, USA)
Ming-Ching Chang (University at Albany, State University of New York, USA)
Siwei Lyu (University at Albany, State University of New York, USA)
MesoNet: a Compact Facial Video Forgery Detection Network (11:10-11:30 AM)
Darius Afchar (école des Ponts Paristech, Marne-la-Vallée, France), Vincent Nozick (UPEM, France)
Junichi Yamagishi (National Institute of Informatics, Tokyo, Japan)
Isao Echizen (National Institute of Informatics, Tokyo, Japan)
Transforming Acoustic Characteristics to Deceive Playback Spoofing Countermeasures of Speaker Verification Systems (11:30-11:50 AM)
Fuming Fang (National Institute of Informatics, Japan)
Junichi Yamagishi (National Institute of Informatics, Japan and University of Edinburgh, UK)
Isao Echizen (National Institute of Informatics, Japan), Md Sahidullah (Inria, France)
Tomi Kinnunen (University of Eastern Finland, Finland)
20 Minutes Oral Presentations (15 Minutes Presentation + 5 Minutes for Q/A and Setup Time)
Oral Session # 2 -Digital Camera Forensics (11:50 AM-12:30 PM)
Session Chair: Chau-Wai Wong (North Carolina State University, USA)
Venue: Conference Room
An Inception-Based Data-Driven Ensemble Approach to Camera Model Identification (11:50 AM-12:10 PM)
Anselmo Ferreira (Shenzhen University, Shenzhen, China), Han Chen (Shenzhen University, Shenzhen, China)
Bin Li (Shenzhen University, Shenzhen, China), Jiwu Huang(Shenzhen University, Shenzhen, China)
Countering the Pooled Triangle Test for PRNU-based camera identification (12:10-12:30 PM)
Mauro Barni (University of Siena, Siena, Italy)
Mariko Nakano-Miyatake (National Polytechnic Institute of Mexico, Mexico)
Héctor Santoyo-García (National Polytechnic Institute of Mexico, Mexico)
Benedetta Tondi (University of Siena, Siena, Italy)
Lunch (12:30 - 14:00)
Venue: PolyU Staff Restaurant (4/F, Communal Building)
IEEE SPS Technical Committee (Info. Forensics & Security)
Venue (Invited Members Only): PQ 703, Mong Man Wai Building
Oral Session # 3 -Data Hiding in Encryption Domain (2:00-3:20 PM)
Session Chair: Mauro Barni (University of Siena, Siena, Italy)
Venue: Conference Room
EPE-based Huge-Capacity Reversible Data Hiding in Encrypted Images (2:00-2:20 PM)
Pauline Puteaux (LIRMM – CNRS, Univ. Montpellier, Montpellier, France)
William Puech (LIRMM – CNRS, Univ. Montpellier, Montpellier, France)
Reversible Data Hiding in Encrypted Images with Two-MSB Prediction (2:20-2:40 PM)
Yi Puyang (Anhui University, Hefei, China and Shanghai University, Shanghai, China)
Zhaoxia Yin (Anhui University, Hefei, China and Purdue University, Indiana, USA)
Zhenxing Qian (Shanghai University, Shanghai, China)
Reversible Contrast Mapping based Reversible Data Hiding in Encrypted Images (2:40-3:00 PM)
Yingqiang Qiu (Huaqiao University, Fujian, China), Hangxing Wang (Huaqiao University, Fujian, China)
Zichi Wang (Shanghai University, Shanghai, China), Zhenxing Qian (Shanghai University, Shanghai, China)
Gui Feng (Huaqiao University, Fujian, China), Xinpeng Zhang (Shanghai University, Shanghai, China)
Camera Attribution Forensic Analyzer in the Encrypted Domain (3:00-3:20 PM)
Alberto Pedrouzo-Ulloa (University of Vigo, Vigo, Spain)
Miguel Masciopinto (University of Vigo, Vigo, Spain)
Juan Ramón Troncoso-Pastoriza (école Polytechnique Fédérale de Lausanne, Lausanne,
Switzerland), Fernando Pérez-González (University of Vigo, Vigo, Spain)
Coffee break (15:20 - 15:40)
Venue: Conference Room Lobby
Oral Session # 4 - Watermarking and Data Hiding (3:40-4:40 PM)
Session Chair: William Puech (LIRMM – CNRS, Univ. Montpellier, Montpellier, France)
Venue: Conference Room
Are Deep Neural Networks good for blind image watermarking? (3:40-4:00 PM)
Vedran Vukotić (Lamark, France), Vivien Chappelier (Lamark, France)
Teddy Furon (Univ Rennes, Inria, CNRS, IRISA, France)
A Multi-Task Learning CNN for Image Steganalysis (4:00-4:20 PM)
Xiangyu Yu (South China University of Technology, China)
Huabin Tan (South China University of Technology, China)
Hui Liang (South China University of Technology, China), Chang-Tsun Li (Charles Sturt University, Australia)
Guangjun Liao (Guangdong Police College, China)
Adaptive Steganography in the Noisy Channel with Dual-Syndrome Trellis Codes (4:20-4:40 PM)
Christy Kin-Cleaves (Oxford University, Oxford, UK), Andrew D. Ker (Oxford University, Oxford, UK)
Oral Session # 5 - Data Protection and Access Control (4:40-5:40 PM)
Session Chair: Fernando Pérez-González (University of Vigo, Vigo, Spain)
Venue: Conference Room
Emotional Bots: Content-based Spammer Detection on Social Media (4:40-5:00 PM)
Panagiotis Andriotis (University of the West of England, Bristol, U.K.)
Atsuhiro Takasu (National Institute of Informatics, Tokyo, Japan)
Protect Your Deep Neural Networks from Piracy (5:00-5:20 PM)
Mingliang Chen (University of Maryland, USA), Min Wu (University of Maryland, USA)
A Randomized Kernel-Based Secret Image Sharing Scheme (5:20-5:40 PM)
Akella Ravi Tej (IIT Roorkee, India), Rekula Raviteja (IIT Roorkee, India)
Vinod Pankajakshan (IIT Roorkee, India)
December 12, 2018
Registration (08:30 -09:30)
Venue: Registration Desk, Reception Area (M1607)
Keynote Talk (09:00 - 10:00)
Keynote Speaker: Joseph Bonneau (New York University, USA)
Hostile Blockchain Takeovers
Venue: Conference Room
Coffee break (10:00 - 10:20)
Venue: Conference Room Lobby
Oral Session # 6 - Privacy Protection and Enhancement (10:20-11:20 AM)
Session Chair: Yi Wang (Dongguan University of Technology, China)
Venue: Conference Room
Latent Feature Disclosure under Perfect Sample Privacy (10:20-10:40 AM)
Borzoo Rassouli (University of Essex, UK), Fernando Rosas (Imperial College London, UK)
Deniz Gündüz (Imperial College London, UK)
Privacy-Preserving Distributed Deep Learning with Privacy Transformations (10:40-11:00 AM)
Sen-ching S. Cheung (University of Kentucky, Lexington, KY, USA)
Muhammad Usman Rafique (University of Kentucky, Lexington, KY, USA)
Wai-tian Tan (Cisco Systems Inc., San Jose, CA, USA)
A Novel Approach For Data Packing: Using Trapdoor Knapsack (11:00-11:20 AM)
Majid Nateghizad (Delft University of Technology, Netherland)
Zekeriya Erkin (Delft University of Technology, Netherland)
Reginald L. Lagendijk (Delft University of Technology, Netherland)
Oral Session # 7 -Fingerprint-based Security and Protection (11:20 AM-12:20 PM)
Session Chair: Richa Singh (IIITD, India)
Venue: Conference Room
One-factor Cancellable Scheme for Fingerprint Template Protection: Extended Feature Vector (EFV) Hashing (11:20-11:40 AM)
Ming Jie Lee (Monash University Malaysia, Malaysia), Zhe Jin (Monash University Malaysia, Malaysia)
Andrew Beng Jin Teoh (Yonsei University, Korea)
Database Binning and Retrieval in Multi-Fingerprint Identification Systems (11:40 AM-12:00 Noon)
P. Drozdowski (Biometrics and Internet Security Research Group, Hochschule Darmstadt, Germany and
NTNU, Norway)
D. Fischer (Biometrics and Internet Security Research Group, Hochschule Darmstadt, Germany)
C. Rathgeb (Biometrics and Internet Security Research Group, Hochschule Darmstadt, Germany)
C. Schielz (Bundeskriminalamt (BKA), Wiesbaden, Germany)
C. Busch (Biometrics and Internet Security Research Group, Hochschule Darmstadt, Germany)
Fingerprint Presentation Attack Detection Using A Novel Multi-Spectral Capture Device and Patch-Based Convolutional Neural Networks (12:00 Noon-12:20 PM)
Mohamed E. Hussein (Information Sciences Institute, CA, USA and Alexandria University, Alexandria, Egypt)
Leonidas Spinoulas (Information Sciences Institute, USC, USA)
Fei Xiong (Information Sciences Institute), Wael Abd-Almageed (Information Sciences Institute, USC, USA)
Lunch (12:20 -13:15)
Venue: PolyU Communal Staff Restaurant (4/F, Communal Building)
Boarding Bus for Social Gathering (13:10 - 13:20)
Social Gathering (15:30 - 18:30)
Banquet Dinner (18:30 - 21:00)
Boarding Bus for Return (21:15 - 21:30)
December 13, 2018
Registration (08:30 -09:30)
Venue: Registration Desk, Reception Area (M1607)
Panel Session
link to presentation (09:00 - 10:00)
Panel Session Chair: Mauro Barni (University of Siena, Siena, Italy)
Venue: Conference Room
Key Research Problems in Information Forensics and Security for the next Five Years
Panelist:
Deniz Gunduz (Imperial College London, London, UK)
Fernando Pérez-González (University of Vigo, Vigo, Spain)
Patrizio Campisi (Roma Tre University, Roma, Italy)
Teddy Furon (Univ Rennes, Inria, CNRS, IRISA, France)
Tobias Oechtering (KTH Royal Institute of Technology, Stockholm, Sweden) link to presentation
TIFS Papers Poster Spotlights (6 Posters)(10:00 - 10:20)
Session Chair: Rafael F. Schaefer (Technische Universität München, Germany)
Venue: Conference Room
"Improving PRNU compression through preprocessing quantization and coding" T-IFS, 2019
Luca Bondi (Politecnico di Milano, Italy), Paolo Bestagini (Politecnico di Milano, Italy)
Fernando Perez-González (University of Vigo, Vigo, Spain), Stefano Tubaro (Politecnico di Milano, Italy)
"Slope authentication at the physical layer" T-IFS, 2018
Ning Xie (Shenzhen University, Shenzhen, China), Changsheng Chen (Shenzhen University, Shenzhen, China)
"Factors affecting ENF capture in audio" T-IFS, 2018
Adi Haji-Ahmad (University of Maryland, College Park, MD, USA)
Chau-Wai Wong (University of Maryland, College Park, MD, USA)
Steven Gambino (Maryland, College Park, MD, USA)
Qiang Zhu (University of Maryland, College Park, MD, USA)
Miao Yu (Maryland, College Park, MD, USA), Min Wu (University of Maryland, College Park, USA)
"Large-scale jpeg image steganalysis using hybrid deep-learning framework" T-IFS, 2018
Jishen Zeng (Shenzhen University, Shenzhen, China), Shunquan Tan (Shenzhen University, Shenzhen, China)
Bin Li (Shenzhen University, Shenzhen, China), Jiwu Huang (Shenzhen University, Shenzhen, China)
"Network traffic fingerprinting based on approximated kernel two-sample test" T-IFS, 2017
Jan Kohout (Czech Technical University in Prague, Prague, Czech Republic)
Tomáš Pevný (Czech Technical University in Prague, Prague, Czech Republic)
"Multi-scale difference map fusion for tamper localization using binary ranking hashing" T-IFS, 2017
Cai-Ping Yan (University of Macau, Macau, China), Chi-Man Pun (University of Macau, Macau, China)
TIFS Poster Session and Coffee break (10:20 - 10:40)
Poster Session (6 Posters)
Venue: Conference Room
Oral Session # 8 - Compression and Authentication (10:40-11:40 AM)
Session Chair: Iuliia Tkachenko (University Lyon, UJM-Saint-Etienne, France)
Venue: New Conference Room TU 201
JPEG Implementation Forensics Based on Eigen-Algorithms (10:40 -11:00 AM)
Nicoló Bonettini (Politecnico di Milano, Italy), Luca Bondi (Politecnico di Milano, Italy)
Paolo Bestagini (Politecnico di Milano, Italy), Stefano Tubaro (Politecnico di Milano, Italy)
Exposing Image Resizing utilizing Welch Power Spectral Density Analysis for Double Compressed JPEG Images (11:00 -11:20 AM)
Sidhant Sahu (NIT Rourkela, India), Manish Okade (NIT Rourkela, India)
Enhanced Geometric Reflection Models for Paper Surface Based Authentication (11:20 -11:40 AM)
Runze Liu (North Carolina State University, USA), Chau-Wai Wong (North Carolina State University, USA)
Min Wu (University of Maryland, College Park, USA)
Oral Session # 9 - Pattern Analysis and Forensics (11:40 AM -12:40 PM)
Session Chair: Bin Li (Shenzhen University, China)
Venue: New Conference Room TU 201
Revealing the processing history of pitch-shifted voice using CNNs (11:40 AM -12:00 Noon)
Lihua Wang (Sun Yat-sen University, Guangzhou, China)
Huixin Liang (Sun Yat-sen University, Guangzhou, China)
Xiaodan Lin (Sun Yat-sen University, Guangzhou, China)
Xiangui Kang (Sun Yat-sen University, Guangzhou, China)
Error Analysis of Forensic ENF Matching (12:00 Noon -12:20 PM)
Guang Hua (Wuhan University, China)
Exploitation of Redundancy for Pattern Estimation of Copy-Sensitive Two Level QR Code (12:20 AM -12:40 PM)
Iuliia Tkachenko (University Lyon, UJM-Saint-Etienne, France), Christophe Destruel (IGO, France)
Lunch (12:40 -14:00)
Venue: PolyU Communal Staff Restaurant (4/F, Communal Building)
Meeting: Editorial Board Meeting (IEEE Transactions on Information Forensics and Security)
Venue (Invited Members Only): PQ 703, Mong Man Wai Building
Oral Session # 10 - Physical Layer Security (14:00 -15:20)
Session Chair: Tobias Oechtering (KTH Royal Institute of Technology, Stockholm, Sweden)
Venue: New Conference Room TU 201
The Deterministic and Correlated Random Public-Confidential Capacity Regions of the Arbitrarily Varying Wiretap Channel (2:00 -2:20 PM)
Ahmed S. Mansour (Technische Universität München, Germany)
Rafael F. Schaefer (Technische Universität München, Germany)
Holger Boche (Technische Universität München, Germany)
Adaptive Channel Estimation in Side Channel Attacks (2:20 -2:40 PM)
Shan Jin (Texas A & M University, USA), Riccardo Bettati (Texas A & M University, USA)
Performance Evaluation of Secure Communication Systems on Turing Machines (2:40 -3:00 PM)
Holger Boche (Technische Universität München, Germany)
Rafael F. Schaefer (Technische Universität München, Germany)
H. Vincent Poor (Princeton University, New Jersey, USA)
Community-based anomaly detection (3:00 -3:20 PM)
Martin Kopp (Cisco Systems, Inc. and Czech Technical University, Prague, Czech Republic)
Martin Grill (Cisco Systems, Inc.)
Jan Kohout (Cisco Systems, Inc. and Czech Technical University, Prague, Czech Republic)
Coffee break (15:20 - 15:40)
Venue: New Conference Room TU 201
Oral Session # 11 - Biometrics Identification (15:40 -17:00)
Session Chair: Andrew Beng Jin Teoh (Yonsei University, Korea)
Venue: New Conference Room TU 201
Gender Effect on Face Recognition for a Large Longitudinal Database (3:40 -4:00 PM)
Caroline Werther (University of North Carolina Wilmington, North Carolina, USA)
Morgan Ferguson (Elon University, North Carolina, USA)
Kevin Park (Emory University, Atlanta, USA)
Troy Kling (University of North Carolina Wilmington, North Carolina, USA)
Cuixian Chen (University of North Carolina Wilmington, North Carolina, USA)
Yishi Wang (University of North Carolina Wilmington, North Carolina, USA)
Finger-vein Recognition using Deep Fully Convolutional Neural Semantic Segmentation Networks: The Impact of Training Data (4:00 -4:20 PM)
Ehsaneddin Jalilian (University of Salzburg, Austria), Andreas Uhl (University of Salzburg, Austria)
Age Estimation via Fusion of Depthwise Separable Convolutional Neural Networks (4:20 -4:40 PM)
Kuan-Hsien Liu (National Taichung University of Science and Technology, Taiwan)
Hsin-Hua Liu (National Taiwan University, Taiwan)
Pak Ki Chan (National Chung Hsing University, Taiwan)
Tsung-Jung Liu (National Chung Hsing University, Taiwan)
Soo-Chang Pei (National Taiwan University, Taiwan)
Generalized Joint Sparse Representation for Multimodal Biometric Fusion of Heterogeneous Features (4:40 -5:00 PM)
Rudi Primorac (The University of Western Australia, Australia)
Roberto Togneri (The University of Western Australia, Australia)
Mohammed Bennamoun (The University of Western Australia, Australia)
Ferdous Sohel (Murdoch University, Australia)
Closing Remarks (17:00 - 17:10)